The Research Behind Billion-Dollar Breaches
Data-driven insights from leading cybersecurity reports.
Real Breaches That Could Have Been Prevented
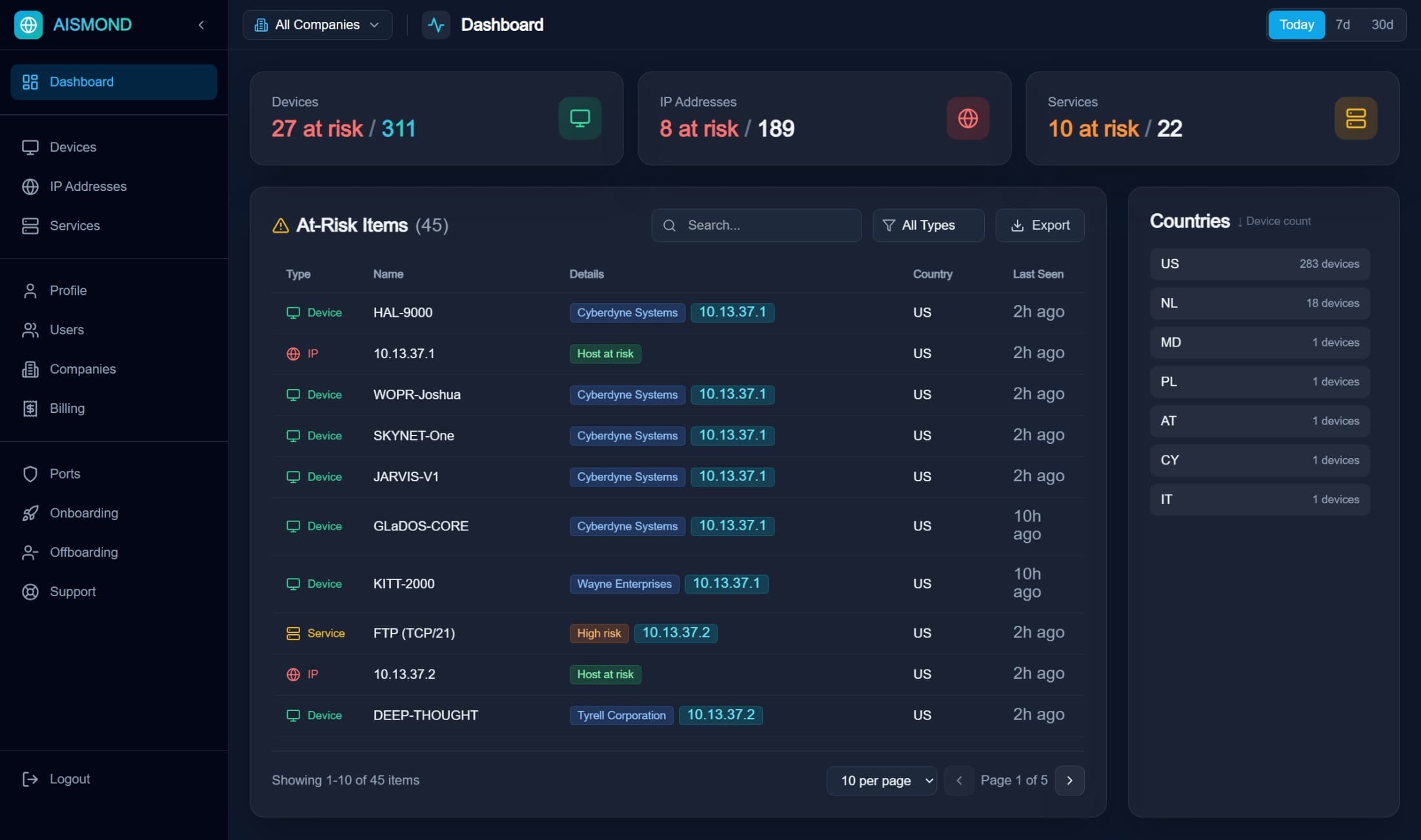
Enterprise-Grade Visibility
Monitor your entire attack surface from a single pane of glass. Identify risks, track exposures, and secure your infrastructure in real-time.
Precision Risk Intelligence
We don't just flag exposures; we analyze them. Our multi-factor algorithm combines community reports, vulnerability databases, threat feeds, and port sensitivity.
Abuse Reports
+45
Active CVEs
+25
Threat Feeds
+15
Dangerous Ports
+10
Risk Score
95
CRITICAL
Complete Attack Surface Monitoring
We monitor everything attackers see and provide intelligence to protect it.
Internet Exposure Detection
Continuous monitoring of what services are exposed to the internet, from RDP ports to web servers
Risk Scoring & Analysis
Intelligent algorithms that score and prioritize security risks based on business impact
Device Discovery & Inventory
Complete visibility into all internet-facing devices and their associated security profiles
Geographic Tracking
Track device locations with precision and detect unauthorized geographic access patterns
Executive Dashboards
Beautiful, comprehensive dashboards showing security posture for leadership and stakeholders
Compliance Documentation
Automated generation of security reports for audits, SOC 2, ISO 27001, and other frameworks